The Auckland Transport (AT) transportation authority in New Zealand is coping with a widespread outage attributable to a cyber incident, impacting a variety of buyer providers.
AT is the government-owned regional transportation authority within the Auckland area, chargeable for public transport via ferries, busses, and trains and for designing and constructing roads and different infrastructure.
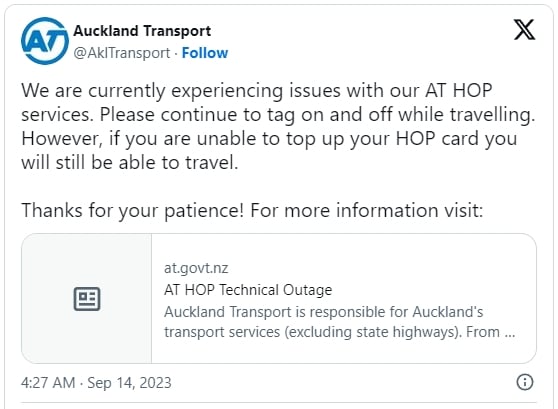
The corporate has introduced at the moment that it is experiencing points with its HOP providers (built-in ticketing and fares system) as a cyber incident has impacted components of its community.
Based on the most recent replace printed earlier at the moment, the next AT providers have been impacted because of the assault:
- On-line top-ups, in addition to different AT HOP providers utilizing MyAT HOP on the AT web site.
- Present auto top-ups work, however there is a delay within the cost processing.
- Ticket and top-up machines are solely accepting money funds.
- Transactions utilizing Eftpos/bank cards are unavailable. Some machines might not be working.
- AT customer support facilities could have restricted performance and will solely be capable to settle for money funds.
- HOP retailers can’t prime up HOP playing cards or course of different AT HOP providers like loading concessions.
In a press release given to native media outlet NZ Herald, a spokesperson for AT acknowledged that they’ve indications they have been focused by ransomware however famous that investigations are nonetheless ongoing.
The identical supply acknowledged that there can be leniency for passengers with empty HOP playing cards, and touring utilizing AT’s busses, ferries, and trains ought to proceed unaffected.
AT’s web site and HOP providers may return to regular operations early subsequent week, so endurance is really helpful because the group progressively restores the affected methods.
Provided that ransomware assaults usually additionally contain information exfiltration for use in double-extortion, there’s concern that AT prospects may need had their delicate particulars uncovered.
Relating to this situation, AT mentions, “At this time limit, we imagine the incident is remoted to 1 a part of our system and that no private or monetary information has been accessed.”
No main ransomware teams have but assumed duty for the assault on AT’s methods.