
The malware loader ‘Bumblebee’ has damaged its two-month trip with a brand new marketing campaign that employs new distribution strategies that abuse 4shared WebDAV providers.
WebDAV (Net Distributed Authoring and Versioning) is an extension of the HTTP protocol that allows shoppers to carry out distant authoring operations corresponding to creating, accessing, updating, and deleting internet server content material.
Intel471’s researchers report that Bumblebee’s newest marketing campaign, which began on September 7, 2023, abuses the 4shared WebDAV providers to distribute the loader, accommodate the assault chain, and carry out a number of post-infection actions.
The abuse of the 4shared platform, a professional and well-known file-hosting providers supplier, helps Bumblebee operators evade blocklists and luxuriate in excessive infrastructure availability.
On the similar time, the WebDAV protocol offers them a number of methods to bypass behavioral detection techniques and the added benefit of streamlined distribution, simple payload switching, and so on.
Spam emails
The present Bumblebee marketing campaign depends on malspam emails that fake to be scans, invoices, and notifications to lure recipients into downloading malicious attachments.
Most attachments are Home windows shortcut LNK information, however there are additionally some ZIP archives containing LNK information, possible an indication that the Bumblebee operators are experimenting to find out what works greatest.
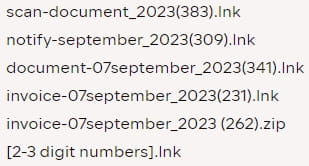
(Intel471)
Opening the LNK file launches a collection of instructions on the sufferer’s machine, beginning with one to mount a WebDAV folder on a community drive utilizing hardcoded credentials for a 4shared storage account.
4Shared is a file-sharing web site that permits customers to retailer information within the cloud and entry them over WebDAV, FTP, and SFTP. The service was beforehand listed within the US authorities’s 2016 Infamous Markets report for the internet hosting of copyrighted content material.
Right here, too, Intel471 noticed a number of variations of the command set, from mounting the file copies, extracting, and executing the information from the mounted drive, which is one other indication of trial for optimization.
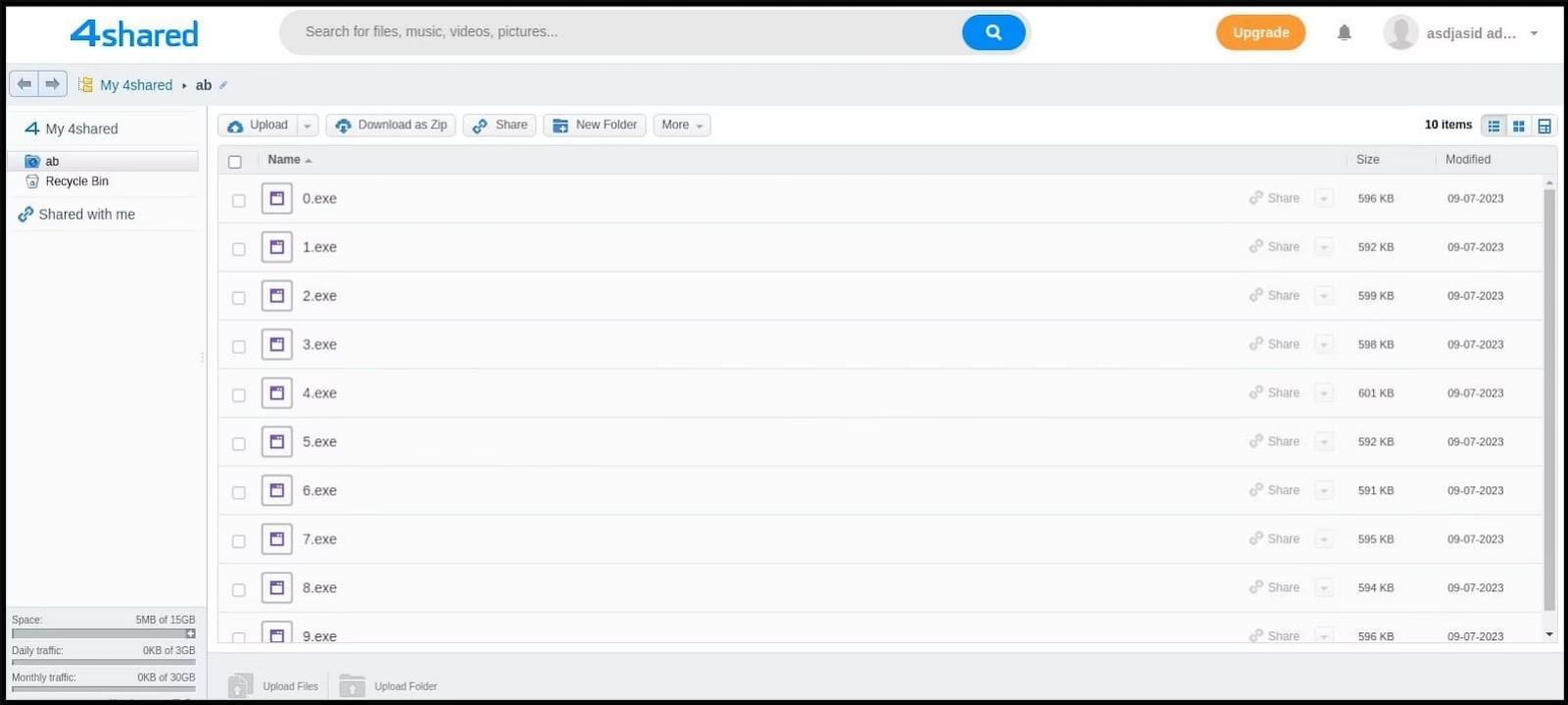
Intel471 reviews seeing the menace actors experimenting with totally different strategies for mounting file copies, extracting, and executing information from the mounted drive, indicating they’re making an attempt to optimize the assault chain.
New Bumblebee
The analysts have additionally noticed an up to date model of the Bumblebee malware loader getting used on this marketing campaign, which has switched from utilizing the WebSocket protocol to TCP for command and management server (C2) communications.
Moreover, the brand new loader has deserted the usage of hardcoded C2 addresses. It now makes use of a site technology algorithm (DGA) to generate 100 domains on the “.life” top-level area (TLD) house upon execution.
The domains are generated utilizing a 64-bit static seed worth, and Bumblebee connects to them by iterating by means of the created listing till it finds one which resolves to an energetic C2 server IP tackle.
Bumblebee has been beforehand related with ransomware payload distribution, together with Conti and Akira, so adopting a extra environment friendly and elusive distribution channel is a worrying growth.
Additionally, adopting DGA makes it more durable to map Bumblebee’s infrastructure, block its domains, and considerably disrupt its operations, including further complexity in implementing preventive motion towards the malware loader.
