Iranian nation-state actors have been conducting password spray assaults in opposition to hundreds of organizations globally between February and July 2023, new findings from Microsoft reveal.
The tech large, which is monitoring the exercise below the title Peach Sandstorm (previously Holmium), mentioned the adversary pursued organizations within the satellite tv for pc, protection, and pharmaceutical sectors to probably facilitate intelligence assortment in help of Iranian state pursuits.
Ought to the authentication to an account achieve success, the menace actor has been noticed utilizing a mix of publicly out there and customized instruments for discovery, persistence, and lateral motion, adopted by knowledge exfiltration in restricted instances.
Peach Sandstorm, additionally identified by the names APT33, Elfin, and Refined Kitten, has been linked to spear-phishing assaults in opposition to aerospace and vitality sectors prior to now, a few of which have entailed using the SHAPESHIFT wiper malware. It is mentioned to be lively since at the very least 2013.

“Within the preliminary section of this marketing campaign, Peach Sandstorm performed password spray campaigns in opposition to hundreds of organizations throughout a number of sectors and geographies,” the Microsoft Risk Intelligence staff mentioned, noting among the exercise is opportunistic.
Password spraying refers to a method whereby a malicious actor makes an attempt to authenticate to many various accounts utilizing a single password or an inventory of commonly-used passwords. It is completely different from brute-force assaults wherein a single account is focused with many credential combos.
“Exercise noticed on this marketing campaign aligned with an Iranian sample of life, notably in late Might and June, the place exercise occurred nearly solely between 9:00 AM and 5:00 PM Iran Normal Time (IRST),” Microsoft additional added.
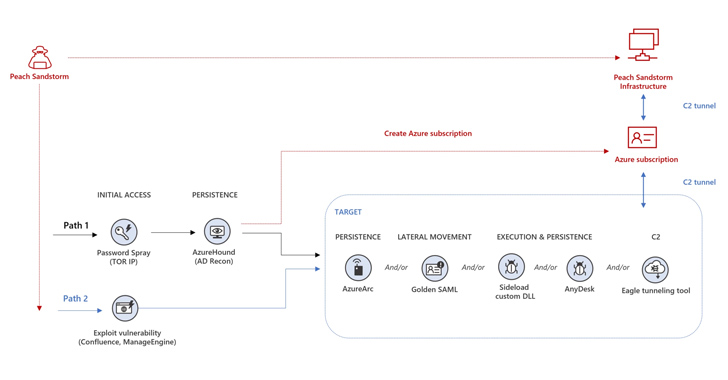
Intrusions are characterised by way of open-source crimson staff instruments reminiscent of AzureHound, a Golang binary to conduct reconnaissance, and ROADtools to entry knowledge in a goal’s cloud surroundings. Moreover, the assaults have been noticed utilizing Azure Arc to ascertain persistence by connecting to an Azure subscription managed by the menace actor.
Alternate assault chains mounted by Peach Sandstorm have entailed the exploitation of safety flaws in Atlassian Confluence (CVE-2022-26134) or Zoho ManageEngine (CVE-2022-47966) to achieve preliminary entry.
Identification is the New Endpoint: Mastering SaaS Safety within the Fashionable Age
Dive deep into the way forward for SaaS safety with Maor Bin, CEO of Adaptive Defend. Uncover why identification is the brand new endpoint. Safe your spot now.
Another notable facets of the post-compromise exercise concern the deployment of AnyDesk distant monitoring and administration instrument to take care of entry, EagleRelay to tunnel site visitors again to their infrastructure, and leveraging Golden SAML assault methods for lateral motion.
“Peach Sandstorm additionally created new Azure subscriptions and leveraged the entry these subscriptions offered to conduct extra assaults in different organizations’ environments,” Microsoft mentioned.
“As Peach Sandstorm more and more develops and makes use of new capabilities, organizations should develop corresponding defenses to harden their assault surfaces and lift prices for these assaults.”
