A novel cloud-native cryptojacking operation has set its eyes on unusual Amazon Net Companies (AWS) choices similar to AWS Amplify, AWS Fargate, and Amazon SageMaker to illicitly mine cryptocurrency.
The malicious cyber exercise has been codenamed AMBERSQUID by cloud and container safety agency Sysdig.
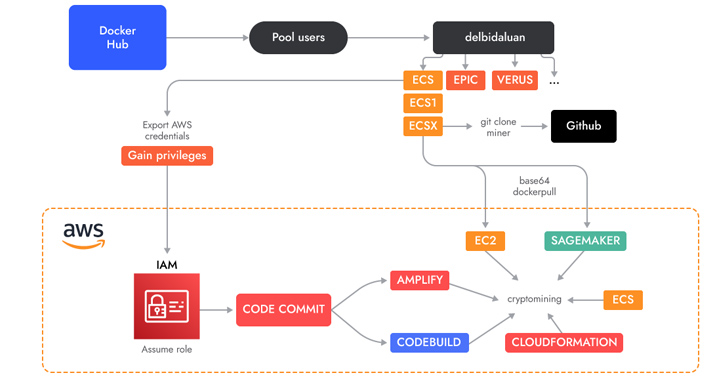
“The AMBERSQUID operation was capable of exploit cloud companies with out triggering the AWS requirement for approval of extra sources, as could be the case in the event that they solely spammed EC2 cases,” Sysdig safety researcher Alessandro Brucato stated in a report shared with The Hacker Information.
“Focusing on a number of companies additionally poses extra challenges, like incident response, because it requires discovering and killing all miners in every exploited service.”

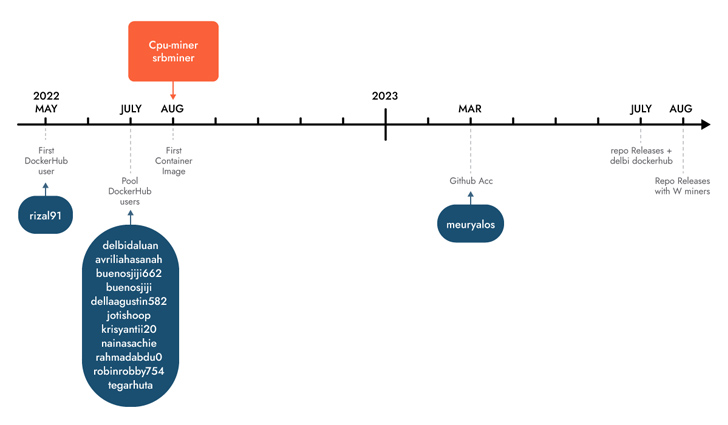
Sysdig stated it found the marketing campaign following an evaluation of 1.7 million photos on Docker Hub, attributing it with average confidence to Indonesian attackers primarily based on using Indonesian language in scripts and usernames.
A few of these photos are engineered to execute cryptocurrency miners downloaded from actor-controlled GitHub repositories, whereas others run shell scripts concentrating on AWS.
A key attribute is the abuse of AWS CodeCommit, which is used to host personal Git repositories, to “generate a personal repository which they then utilized in completely different companies as a supply.”
The repository incorporates the supply code of an AWS Amplify app that, in flip, is leveraged by a shell script to create a Amplify net app and in the end launch the cryptocurrency miner.
The menace actors have additionally been noticed using shell scripts to carry out cryptojacking in AWS Fargate and SageMaker cases, incurring vital compute prices for the victims.
Sysdig estimated that AMBERSQUID may end in losses of greater than $10,000 per day if it is scaled to focus on all AWS areas. An additional evaluation of the pockets addresses used reveals that the attackers have earned greater than $18,300 in revenues thus far.
Identification is the New Endpoint: Mastering SaaS Safety within the Trendy Age
Dive deep into the way forward for SaaS safety with Maor Bin, CEO of Adaptive Defend. Uncover why id is the brand new endpoint. Safe your spot now.
This isn’t the primary time Indonesian menace actors have been linked to cryptojacking campaigns. In Might 2023, Permiso P0 Labs detailed an actor named GUI-vil which was noticed leveraging Amazon Net Companies (AWS) Elastic Compute Cloud (EC2) cases to hold out crypto mining operations.
“Whereas most financially motivated attackers goal compute companies, similar to EC2, it is very important keep in mind that many different companies additionally present entry to compute sources (albeit it extra not directly),” Brucato stated.
“It’s straightforward for these companies to be missed from a safety perspective since there’s much less visibility in comparison with that out there by means of runtime menace detection.”