
The latest Gcore Radar report and its aftermath have highlighted a dramatic enhance in DDoS assaults throughout a number of industries. Firstly of 2023, the typical power of assaults reached 800 Gbps, however now, even a peak as excessive as 1.5+ Tbps is unsurprising. To try to break by Gcore’s defenses, perpetrators made two makes an attempt with two completely different methods. Learn on to find what occurred and find out how the safety supplier stopped the attackers of their tracks with out affecting finish customers’ experiences.
A Highly effective DDoS Assaults
In November 2023, certainly one of Gcore’s prospects from the gaming business was focused by two large DDoS assaults, peaking at 1.1 and 1.6 Tbps respectively. The attackers deployed varied methods in an unsuccessful try and compromise Gcore’s protecting mechanisms.
Assault #1: 1.1 Tbps UDP-based DDoS
Within the first cyber assault, the attackers despatched a barrage of UDP visitors to a goal server, peaking at 1.1 Tbps. Two strategies had been employed:
- By utilizing random UDP supply ports, they hoped to evade typical filtering mechanisms.
- The attackers hid their real identification by forging supply IP addresses.
This was a traditional flood (or volumetric) assault, whereby the attackers hoped to eat all accessible bandwidth of or to a knowledge heart or community, overwhelming the goal servers with visitors and making them unavailable to reliable customers.
The graph under exhibits buyer’s visitors throughout the assault. The height of 1.1 Tbps exhibits an aggressive however short-lived try and flood the community with knowledge. The inexperienced line (“whole.normal.enter”) exhibits all inbound visitors. The opposite coloured traces on the graph characterize the community’s responses, together with measures to filter and drop malicious visitors, because the system manages the deluge of knowledge.
 |
| The assault comprised a brief however intense peak of 1.1 Tbps round 22:55 |
Assault #2: 1.6 Tbps TCP-based DDoS
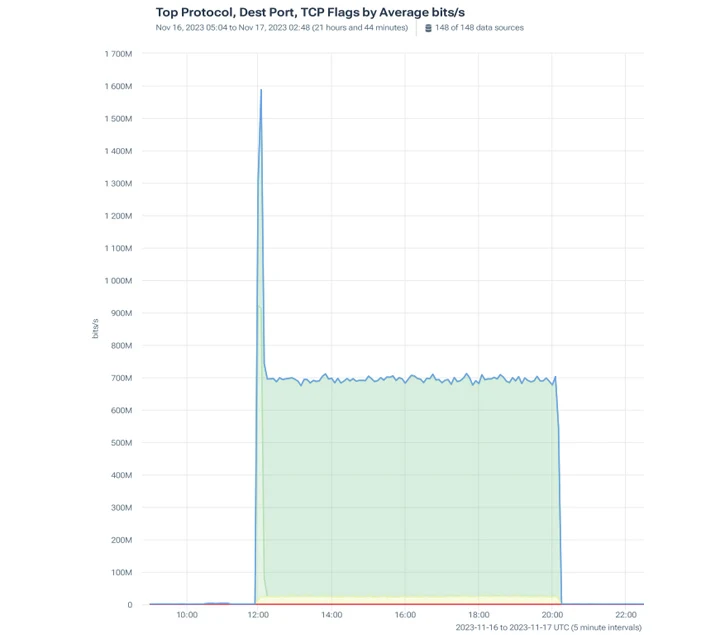 |
| The assault’s constant visitors quantity was 700 Mbps and on the onset peaked at 1600 Mbps |
This time, the attackers tried to use TCP protocol with a mixture of SYN flood, PSH, and ACK visitors.
In a SYN flood assault, a number of SYN packets are delivered to the goal server with out ACK packets. This implies the server generates a half-open connection for every SYN packet. If profitable, the server will finally run out of assets and cease accepting connections.
The PSH, ACK part of the assault quickly sends knowledge to the goal system. The ACK flag alerts that the server obtained the earlier packet. This pushes the system to deal with knowledge promptly, losing assets. A SYN flood assault utilizing PSH, ACK packets is more durable to defend towards than a SYN flood, for the reason that PSH flag causes the server to course of the packet contents instantly, consuming extra assets.
As earlier than, the aim was to overload the client’s servers and make their companies inaccessible to approved customers. This SYN flood had a peak quantity of 685.77 Mbps and the PSH, ACK had a magnitude of 906.73 Mbps.
Gcore’s Defensive Methods
Gcore’s DDoS Safety successfully neutralized each assaults whereas preserving common service for the client’s finish customers. The final method of warding off DDoS safety threats consists of a number of methods, equivalent to Gcore’s front-line defenses:
- Dynamic visitors shaping: Dynamically adjusted visitors charges successfully mitigate the affect of the assault whereas guaranteeing the continuity of crucial companies. In an effort to prioritize real visitors whereas slowing dangerous transmissions, adaptive thresholds and charge restrictions are used.
- Anomaly detection and quarantine: Fashions based mostly on machine studying analyze conduct to establish anomalies. When an anomaly happens, automated quarantine mechanisms redirect misguided visitors to remoted segments for extra evaluation.
- Common expression filters: To dam malicious payloads with out disrupting reliable visitors, common expression-based filter guidelines are carried out. Their steady fine-tuning ensures optimum safety with out false positives.
- Collaborative menace intelligence: Gcore actively engages within the trade of menace intelligence with business friends. Collective insights and real-time menace feeds information Gcore’s safety methods, permitting a fast response to creating assault vectors.
By using these methods, Gcore was capable of successfully mitigate the affect of DDoS assaults and shield their buyer’s platform from disruption, negating potential reputational and monetary losses.
Conclusion
DDoS assaults of 1.5+ Tbps quantity pose an rising hazard throughout industries, with attackers utilizing imaginative methods to try to bypass safety companies. Over the course of 2023, Gcore has registered will increase in each common and most assault volumes, and these two related assaults exhibit that development.
Within the assaults lined within the article, Gcore was capable of stop any harm by a mix of dynamic visitors shaping, anomaly detection, common expression filters, and collaborative menace intelligence. Discover DDoS Safety choices to safe your community towards ever-evolving DDoS threats.
